Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
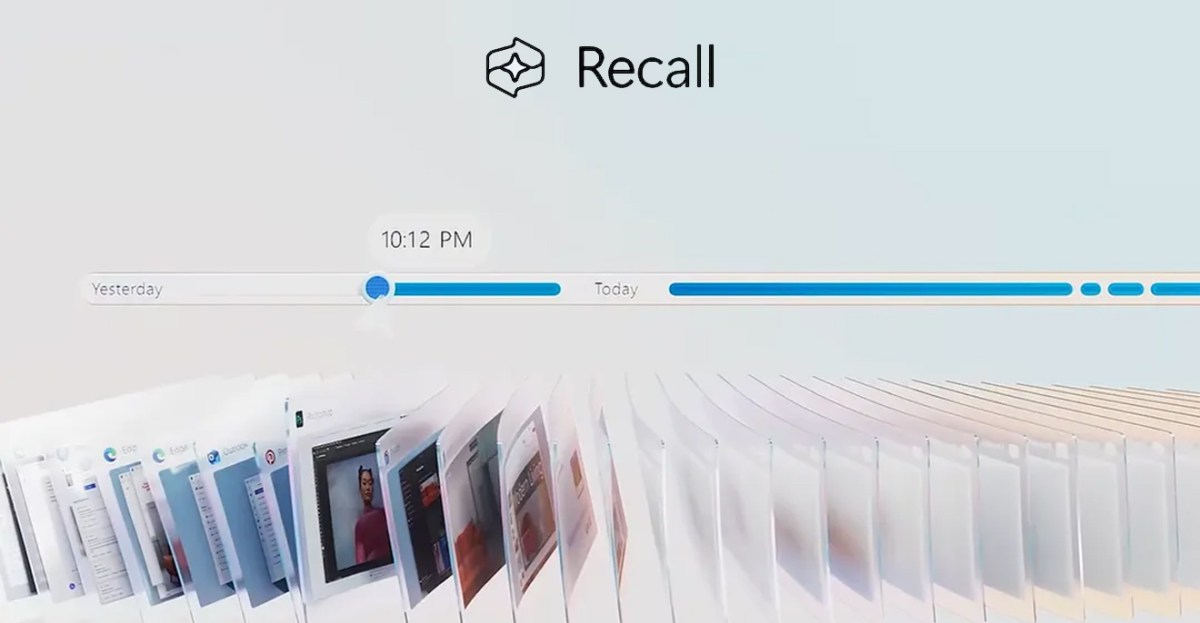
When Microsoft tried to launch Recall, an AI-powered Windows feature that takes screenshots of most of what you do on your computer, that was it. Described as a “disaster” Cybersecurity and the “privacy nightmare.” After the backlash and One year delay To redesign and secure Recall, it again faces security and privacy concerns.
Created by cybersecurity expert Alexander Hagina TotalRecall has been reloadeda tool that extracts data from Recall and displays it. It is an update to TotalRecall that exposed all the vulnerabilities of the original Recall feature before Microsoft redesigned it.
Microsoft’s redesign focused on creating a secure store of recall data, with Windows Hello authentication and a secure environment through a virtualization-based security zone. The recall requires users to authenticate using their face or fingerprint to access data and to enable snapshot recording. “This restricts attempts by latent malware that attempts to ‘match’ user authentication to steal data,” Microsoft said in a statement. September 2024 blog post.
“My research shows that the vault is real, but the limits of trust expire very early,” Hagenah says. “TotalRecall Reloaded makes ‘lurking malware’ go all the way.” The TotalRecall Reloaded tool can run silently in the background and activate the recall timeline to force the user to authenticate using a Windows Hello prompt. Once authentication is performed, TotalRecall Reloaded can then extract everything Windows Recall has captured. “This is exactly the scenario that Microsoft’s architecture is supposed to constrain.” Hagina says.
Recall stores a lot more than just screenshots, it contains a history of the text that appeared on your screen, messages, emails, documents, browsing history, and much more. Microsoft’s security recall changes came months after CEO Satya Nadella He told the staff “If you are facing a trade-off between security and another priority, your answer is clear: do security.”
Hagina responsibly disclosed its latest findings to Microsoft last month, but the company closed the report and said there was no security vulnerability. “We appreciate Alexander Hagina for identifying and responsibly reporting this issue. After careful investigation, we determined that the access patterns described are consistent with our intended protections and existing controls, and do not represent a security breach or unauthorized access to data,” David Weston, vice president of Microsoft Security, says in a statement to Edge. “The authorization period has timeout and hijacking protection, which limits the impact of malicious queries.”
In letters to EdgeHagenah disputes the time-out protection offered by Microsoft. “I can repolle the data, and what I do in my tool is bypass it,” Hagenah says. “And the timeout is corrected.” “My biggest issue still is that they say in their official announcement that the zone prevents the spread of latent malware, which it clearly doesn’t.”
TotalRecall Reloaded can also extract the latest cached Windows Recall screenshot without Windows Hello authentication, or clearing the entire capture history. But the type of malware Hagenah describes can stay in the background on your computer and take screenshots anyway, with or without Windows Recall.
Microsoft does not believe there is a vulnerability here because this is simply the way Windows works. Regular user mode processes have the ability to inject code into themselves as normal and often legitimate behavior in Windows, but this flexibility also creates opportunities for abuse.
Similar information-stealing malware can settle in and extract your 1Password data or browsing history, if undetected by various Windows security tools and memory protection efforts. The biggest concern is that Recall stores much more sensitive data than just passwords or browsing history, and Microsoft’s original promise that Recall would protest malware running in the background.
Despite the concerns, Microsoft did a lot of things right when it came to redesigning the recall process. “The VBS area is very solid,” Hagenah says. “Stateless, race-free authentication model (thousands of sensors, zero abuses).” Hagenah believes Microsoft can and should go a step further to achieve Recall’s security design goals. “The fundamental problem is not cryptocurrencies, enclave, authentication or PPL,” he says. “It’s sending decrypted content to an unprotected display. The vault door is made of titanium. The wall next to it is made of drywall.”